How to Use Prophylaxis to Prevent Your Opponent’s Plans delves into the proactive world of strategic thinking, a realm where anticipating and neutralizing your adversary’s moves is key to success. This isn’t about reacting to threats; it’s about anticipating them, setting the stage, and shaping the outcome to your advantage.
This guide will equip you with the knowledge to identify potential threats, understand the different types of prophylactic measures available, and assess the risks associated with your opponent’s plans. Whether you’re navigating the competitive landscape of business, sports, or any other field, the principles of prophylaxis offer a powerful advantage, turning potential setbacks into opportunities for strategic wins.
Understanding the Core Concept: Prophylaxis in Strategy
Prophylaxis, in a strategic context, is the art of proactively preventing an opponent from achieving their goals. It’s about anticipating potential threats and taking pre-emptive measures to neutralize them before they materialize. This contrasts sharply with reactive strategies, which respond to events after they’ve occurred, often at a disadvantage.
Defining Prophylaxis in Strategic Terms
Prophylaxis involves anticipating and mitigating risks. It’s not merely about reacting to an opponent’s moves; it’s about influencing the game to prevent those moves from ever happening or minimizing their impact. This approach focuses on foresight, preparation, and control, aiming to shape the environment to one’s advantage.
Examples of Prophylactic Strategies Across Different Fields
Prophylactic strategies manifest differently depending on the field of application.
- Business: A company anticipating a competitor’s product launch might proactively invest in research and development to create a superior product, or secure exclusive distribution agreements to limit the competitor’s market access. For instance, in the early 2000s, Microsoft’s aggressive bundling of Internet Explorer with Windows, a prophylactic move against Netscape Navigator, is a classic example of preemptive market control.
This strategic decision severely hampered Netscape’s growth and market share.
- Sports: In soccer, a defensive midfielder might position themselves to intercept passes before they reach the opposing team’s attacking players. In chess, a player might make moves to control key squares or prevent the opponent from developing a strong attack. A well-executed example is the defensive strategy employed by Chelsea FC under José Mourinho, where they prioritized a solid defensive setup to nullify the attacking threats of their opponents, effectively controlling the game’s flow and preventing goal-scoring opportunities.
- Politics: A political campaign might conduct opposition research to uncover potential vulnerabilities of their opponent, proactively addressing these issues through public statements or advertising before they can be exploited. This proactive approach aims to shape public perception and preemptively neutralize any damaging revelations. The Clinton campaign in 1992, famously responding to allegations of extramarital affairs before they became a major news story, is a case in point.
Advantages of Prophylaxis Over Reactive Strategies
Prophylactic strategies offer several key advantages over reactive approaches.
- Control: Prophylaxis allows for greater control over the situation. By taking the initiative, one can dictate the terms of engagement and shape the environment to one’s advantage.
- Reduced Risk: Preemptive measures can significantly reduce the risk of negative outcomes. By anticipating threats and mitigating them early, the potential damage is minimized.
- Efficiency: Prophylaxis can be more efficient than reactive strategies. Responding to a crisis often requires more resources and time than preventing it in the first place.
- Psychological Advantage: Proactive measures can demoralize the opponent by demonstrating preparedness and foresight. This can create a psychological advantage, making them more hesitant and less confident in their plans.
Prophylaxis is about shaping the future, not just reacting to it.
Identifying Opponent’s Plans
Understanding your opponent’s plans is crucial for effective prophylaxis. By anticipating their moves, you can proactively counter them, minimizing their impact and maximizing your own strategic advantage. This section delves into techniques for gathering intelligence and predicting your opponent’s likely actions.
Intelligence Gathering Techniques
Gathering information about your opponent’s intentions involves various methods, from direct observation to indirect analysis. The more comprehensive your intelligence, the better equipped you are to formulate effective prophylactic measures.* Observation and Analysis of Actions: Carefully watch your opponent’s actions. Note their resource allocation, deployment of units, and any apparent shifts in strategy.
Analyzing Communication
Pay attention to their communications, including public statements, internal memos (if accessible), and interactions with allies. These communications often reveal strategic goals and intentions.
Exploiting Weaknesses
Identify and exploit any vulnerabilities in your opponent’s information security or operational procedures to gain insights into their plans.
Utilizing Allies and Networks
Leverage relationships with allies, informants, or intelligence networks to gather information.
Monitoring Activity Patterns
Track your opponent’s routine activities and patterns of behavior. Any deviation from the norm could signal a planned change in strategy.
Predicting Opponent’s Likely Moves
Predicting your opponent’s moves is not an exact science, but by analyzing their past behavior and current context, you can make informed assessments.* Reviewing Past Behavior: Examine your opponent’s historical actions in similar situations. Their past decisions and strategies provide valuable insights into their likely future responses. For example, consider a chess player who consistently favors aggressive openings.
When facing this player, anticipating an aggressive approach is reasonable, allowing you to prepare defensive strategies or counterattacks.
Assessing Current Context
Analyze the current environment, including resource availability, political landscape, and any external pressures on your opponent. These factors influence their decision-making process.
Identifying Key Objectives
Determine your opponent’s primary goals and objectives. Understanding their motivations helps you predict their likely strategies and tactics.
Anticipating Reaction to your actions
Consider how your actions will influence your opponent’s reaction. A successful preemptive strike will usually provoke an opponent to respond with a counterattack.
Modeling Opponent’s Decision-Making
Try to model your opponent’s decision-making process. Consider their risk tolerance, biases, and preferred strategies.
Warning Signs of a Specific Plan
Certain indicators may suggest your opponent is preparing a specific plan. Recognizing these warning signs allows you to initiate prophylactic measures before the plan is fully implemented.* Unusual Resource Mobilization: A sudden increase in resource allocation, such as military deployments, financial investments, or personnel movements, can signal an impending operation.
Changes in Communication Patterns
Alterations in communication frequency, channels, or content may indicate that a plan is in development.
Shifting Alliances
New alliances or strained relationships with existing partners may indicate a shift in strategic goals.
Increased Reconnaissance Activity
An increase in intelligence gathering, such as surveillance, probing attacks, or reconnaissance missions, can indicate preparation for an offensive.
Changes in Routine
Any deviations from an opponent’s normal routine or behavior patterns should be viewed with suspicion.
Public Posturing and Propaganda
Increased rhetoric, aggressive public statements, or disinformation campaigns may be used to create a diversion or prepare the ground for an attack.
Increased Security Measures
Heightened security protocols, such as increased patrols, restricted access, or enhanced surveillance, could indicate a specific plan is in motion.
Sudden Shifts in Strategic Focus
An abrupt change in the opponent’s priorities or objectives suggests a new plan is being developed.
Changes in Training and Exercises
Conducting specialized training exercises or simulations that are outside the norm could signal preparation for a particular operation.
Cyber Attacks or Information Warfare
The use of cyberattacks, phishing attempts, or the spread of misinformation can be used to create confusion or to pave the way for a physical attack.
Types of Prophylactic Measures
Prophylactic measures in strategy can be broadly categorized into offensive and defensive approaches. Offensive strategies aim to preemptively disrupt or eliminate an opponent’s plans, while defensive strategies focus on safeguarding against potential attacks or setbacks. Both types are crucial for maintaining a strategic advantage and minimizing risk. Understanding the nuances of each approach allows for a more comprehensive and adaptable strategic posture.
Comparing Offensive and Defensive Prophylactic Strategies
The following table provides a comparison of offensive and defensive prophylactic strategies, highlighting their key characteristics, objectives, and examples. This comparison will help clarify the distinct roles each strategy plays in preemptively mitigating threats and securing advantages.
| Characteristic | Offensive Prophylaxis | Defensive Prophylaxis | Objective | Example |
|---|---|---|---|---|
| Primary Focus | Preemptively disrupting or eliminating the opponent’s plans. | Protecting against potential attacks or setbacks. | To gain an advantage by preventing the opponent’s actions. | To maintain stability and minimize losses. |
| Action | Active, proactive measures to shape the strategic landscape. | Reactive, safeguarding measures to absorb or deflect attacks. | Create opportunities for oneself by denying them to the opponent. | Preserve resources and strategic position. |
| Risk Profile | Higher risk, higher reward. Potential for significant gains but also for failure. | Lower risk, lower reward. Focus on risk mitigation rather than aggressive expansion. | Aggressive actions aimed at disrupting the opponent. | Conservative actions aimed at preventing damage. |
| Strategic Goal | Control the initiative and dictate the terms of engagement. | Preserve existing advantages and limit the opponent’s influence. | Control the game by controlling the opponent. | Control the game by protecting oneself. |
Offensive Prophylactic Measures
Offensive prophylactic measures are designed to proactively thwart an opponent’s actions. These strategies aim to gain a strategic advantage by disrupting the opponent’s plans before they can be implemented. Success in offensive prophylaxis often involves anticipating the opponent’s moves and acting preemptively.Here are some examples of offensive prophylactic measures:
- Preemptive Strikes: This involves launching an attack or taking an action before the opponent can initiate their plan. For example, in chess, a player might launch an early attack on the opponent’s king to prevent the opponent from developing their pieces effectively. This forces the opponent into a defensive posture, thereby controlling the flow of the game.
- Resource Denial: Limiting the opponent’s access to crucial resources. This can include disrupting supply lines, targeting infrastructure, or forming alliances to isolate the opponent. For instance, during World War II, the Allied forces targeted German oil production facilities, hindering their ability to fuel their military operations.
- Information Warfare: This involves using intelligence and disinformation to confuse, mislead, or demoralize the opponent. Spreading false information about troop movements or economic conditions can create uncertainty and disrupt the opponent’s decision-making process.
- First-Mover Advantage: Taking the initiative to control key territories or strategic positions. In a business context, this could involve launching a new product or service before a competitor, thereby capturing market share and establishing brand recognition.
Defensive Prophylactic Measures
Defensive prophylactic measures are implemented to protect against potential attacks or setbacks. These strategies prioritize risk mitigation and aim to minimize losses, preserving existing advantages. Effective defensive prophylaxis involves identifying vulnerabilities and creating barriers to protect against threats.Here are some examples of defensive prophylactic measures:
- Fortification: Strengthening defenses to withstand attacks. This can involve building physical barriers, like walls or bunkers, or implementing cybersecurity measures to protect digital assets. For example, military fortifications like the Maginot Line were built to deter potential invasions.
- Counterintelligence: Gathering information about the opponent’s plans to identify potential threats and vulnerabilities. This enables proactive responses to prevent or mitigate attacks. This involves a continuous process of gathering, analyzing, and protecting sensitive information.
- Diversification: Spreading resources and investments across multiple areas to reduce the impact of any single setback. This is a common practice in financial markets, where investors diversify their portfolios to mitigate risk.
- Contingency Planning: Developing backup plans to address potential problems. This involves anticipating potential risks and creating plans to respond to them. This could involve having a secondary supply chain or having backup servers.
Assessing Risk and Prioritizing Prophylactic Actions
Effectively mitigating your opponent’s plans requires a systematic approach. This involves not only identifying potential threats but also evaluating their severity and likelihood. Furthermore, it necessitates prioritizing prophylactic actions based on the risks they address and the resources available. This section Artikels a framework for risk assessment and prioritization in the context of strategic prophylaxis.
Organizing a Framework for Assessing Potential Risks
Risk assessment is the cornerstone of proactive strategic planning. It allows you to anticipate potential problems before they arise and allocate resources efficiently. This framework provides a structured approach to analyzing risks.
- Identify Potential Threats: Begin by meticulously listing all possible actions your opponent might take. Consider their strengths, weaknesses, and typical strategies. For example, in a chess game, a potential threat could be a knight fork targeting your queen and rook. In a business negotiation, it could be a competitor undercutting your price.
- Determine the Impact: For each identified threat, assess the potential impact. How damaging would it be if the threat materialized? Quantify the impact whenever possible. This could be in terms of financial loss, reputational damage, or loss of strategic advantage. For instance, the knight fork in chess results in material loss, while a price undercut could reduce your profit margins.
- Assess the Likelihood: Evaluate the probability of each threat occurring. Consider factors such as your opponent’s past behavior, their current resources, and the context of the situation. Is the opponent likely to employ this tactic? Is it within their capabilities? Is the environment conducive to their success?
- Calculate the Risk Score: Combine the impact and likelihood to determine a risk score. A simple method is to multiply the impact (e.g., on a scale of 1-10, where 10 is the most damaging) by the likelihood (e.g., also on a scale of 1-10, where 10 is the most probable). The resulting score provides a basis for prioritizing prophylactic actions. A high score indicates a high-priority risk.
- Regularly Review and Update: Risk assessment is not a one-time exercise. Regularly review and update your assessments as the situation evolves. New information, changes in your opponent’s behavior, or shifts in the environment can alter the risks you face.
Identifying Factors to Consider When Prioritizing Prophylactic Actions
Prioritizing prophylactic actions is critical for efficient resource allocation. It ensures that you address the most significant threats first. Several factors influence this prioritization.
- Risk Score: The primary factor should be the risk score derived from your risk assessment. Higher scores indicate higher priority. Address threats with the highest scores first.
- Cost of Prophylactic Action: Consider the resources required to implement each prophylactic measure. This includes financial costs, time investment, and the potential impact on your own strategic goals. Some measures might be very effective but too costly to justify.
- Effectiveness of the Action: Evaluate how effectively each prophylactic measure mitigates the identified risk. Does it completely eliminate the threat, or does it only reduce its impact or likelihood? Choose actions that offer the greatest risk reduction.
- Availability of Resources: Prioritize actions that align with your available resources. If you have limited resources, focus on the most critical threats and choose the most cost-effective prophylactic measures.
- Strategic Alignment: Ensure that your prophylactic actions align with your overall strategic goals. Avoid measures that, while effective, might inadvertently undermine your broader objectives. For example, a defensive move in chess that protects a pawn but weakens your attack might not be strategically sound.
- Flexibility and Adaptability: Choose prophylactic actions that offer flexibility and adaptability. The situation might change, and you might need to adjust your strategy. Measures that are easily modified or replaced are preferable.
Creating a Risk Assessment Matrix
A risk assessment matrix is a valuable tool for visualizing and organizing your risk assessment. It provides a clear and concise overview of potential threats, their impact, likelihood, and risk scores.
The matrix typically uses a grid format. One axis represents the impact of the threat, and the other axis represents the likelihood of the threat occurring. Each cell in the matrix represents a combination of impact and likelihood, and the color-coding is used to represent the risk score.
Here’s a simplified example of a 3×3 risk assessment matrix:
| Low Likelihood | Medium Likelihood | High Likelihood | |
|---|---|---|---|
| High Impact | High Risk | High Risk | Medium Risk |
| Medium Impact | Medium Risk | Medium Risk | Medium Risk |
| Low Impact | Low Risk | Medium Risk | Medium Risk |
Using the Matrix:
- Identify Threats: List all potential threats in a separate document.
- Assess Impact and Likelihood: For each threat, determine its impact (e.g., low, medium, high) and its likelihood (e.g., low, medium, high).
- Plot the Risk: Locate the corresponding cell in the matrix based on the impact and likelihood.
- Color-Code the Risks: Use the color-coding to represent the risk level. Red indicates high risk, orange indicates medium risk, and green indicates low risk.
- Prioritize Prophylactic Actions: Focus on addressing the threats in the red cells first. Develop prophylactic measures to reduce the impact or likelihood of these high-risk threats.
Example in a Business Context:
Imagine a company launching a new product. They could create a risk assessment matrix. One threat might be a competitor launching a similar product at a lower price (High Impact, Medium Likelihood = Orange/Medium Risk). Another might be a delay in the supply chain (Medium Impact, Medium Likelihood = Orange/Medium Risk). A third could be negative customer reviews (High Impact, Low Likelihood = Yellow/Medium Risk).
Based on the matrix, the company would prioritize prophylactic actions like securing a reliable supply chain, preparing a price-matching strategy, and proactively managing customer feedback.
The risk assessment matrix allows for a clear visualization of priorities, facilitating better decision-making and resource allocation in risk management.
Methods for Implementing Prophylaxis: Tools and Techniques

Implementing prophylactic measures effectively requires a blend of strategic thinking, specialized tools, and well-defined procedures. The choice of methods varies significantly depending on the field, the nature of the threat, and the resources available. This section explores diverse tools and techniques, along with step-by-step procedures and potential challenges.
Information Gathering and Analysis
Before implementing any prophylactic measure, gathering and analyzing information is crucial. This involves understanding the opponent’s potential plans, identifying vulnerabilities, and assessing the risks involved.
- Intelligence Gathering: This involves collecting information from various sources, including open-source intelligence (OSINT), human intelligence (HUMINT), and signals intelligence (SIGINT). For example, in cybersecurity, OSINT might involve monitoring social media for phishing campaigns, while HUMINT could involve analyzing employee behavior for insider threats.
- Vulnerability Assessment: This process identifies weaknesses in a system or process that an opponent could exploit. In project management, this could involve analyzing the project plan for potential bottlenecks or dependencies that could be exploited to delay the project.
- Risk Assessment: This involves evaluating the likelihood and impact of potential threats. In finance, this might involve assessing the risk of a market downturn and its potential impact on investments. A risk matrix is often used to visually represent these assessments.
Cybersecurity Prophylactic Measures
Cybersecurity relies heavily on prophylactic measures to protect systems and data from attacks. These measures are constantly evolving to counter new threats.
- Firewalls: Firewalls act as a barrier between a trusted internal network and an untrusted external network, such as the internet. They filter network traffic based on predefined rules, blocking unauthorized access.
- Step-by-step Procedure:
- Install and configure the firewall software or hardware.
- Define security policies, including allowed and denied traffic based on source/destination IP addresses, ports, and protocols.
- Regularly update the firewall’s software and rule sets to address new vulnerabilities and threats.
- Monitor firewall logs for suspicious activity, such as unauthorized access attempts.
- Potential Pitfalls: Improper configuration can leave vulnerabilities. Outdated software can expose the system to exploits.
- Step-by-step Procedure:
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): These systems monitor network traffic for malicious activity. IDS detects and alerts, while IPS actively blocks malicious traffic.
- Step-by-step Procedure:
- Install and configure the IDS/IPS software or hardware.
- Define security policies, including rules for detecting and preventing malicious activity based on signatures, anomalies, and behavior analysis.
- Regularly update the IDS/IPS’s signature database to detect new threats.
- Monitor the IDS/IPS logs for alerts and take appropriate action.
- Potential Pitfalls: False positives can generate unnecessary alerts, and false negatives can allow attacks to slip through.
- Step-by-step Procedure:
- Endpoint Protection: This includes antivirus software, endpoint detection and response (EDR) solutions, and other tools that protect individual devices.
- Step-by-step Procedure:
- Install endpoint protection software on all devices.
- Configure the software to scan for malware and other threats.
- Regularly update the software’s virus definitions and other security updates.
- Monitor the endpoint protection logs for alerts and take appropriate action.
- Potential Pitfalls: Outdated software can be vulnerable to exploits. Insufficient scanning can miss threats.
- Step-by-step Procedure:
- Data Encryption: Encryption transforms data into an unreadable format, protecting it from unauthorized access.
- Step-by-step Procedure:
- Choose an encryption algorithm, such as AES (Advanced Encryption Standard).
- Generate or obtain encryption keys.
- Encrypt sensitive data at rest (stored data) and in transit (data being transmitted).
- Securely manage the encryption keys.
- Potential Pitfalls: Lost or compromised encryption keys can render data inaccessible. Weak encryption algorithms can be easily broken.
- Step-by-step Procedure:
Financial Risk Management Prophylactic Measures
Financial institutions employ various prophylactic measures to protect against financial risks, such as fraud, market volatility, and credit defaults.
- Diversification: Spreading investments across different asset classes, industries, and geographic regions reduces the impact of any single investment’s poor performance.
- Step-by-step Procedure:
- Assess the investor’s risk tolerance and financial goals.
- Determine the appropriate asset allocation based on risk tolerance and goals.
- Select a diversified portfolio of investments.
- Regularly rebalance the portfolio to maintain the desired asset allocation.
- Potential Pitfalls: Diversification does not eliminate risk; it only reduces it. Market fluctuations can still impact the overall portfolio.
- Step-by-step Procedure:
- Hedging: Using financial instruments, such as derivatives, to offset potential losses from adverse market movements.
- Step-by-step Procedure:
- Identify the risk to be hedged (e.g., currency risk, interest rate risk).
- Select the appropriate hedging instrument (e.g., forward contract, option).
- Determine the size of the hedge.
- Monitor the hedge and adjust it as needed.
- Potential Pitfalls: Hedging can be expensive and may not completely eliminate risk. Improper hedging can lead to losses.
- Step-by-step Procedure:
- Stress Testing: Simulating extreme market scenarios to assess the potential impact on a financial institution’s portfolio and capital.
- Step-by-step Procedure:
- Define the stress scenarios (e.g., a major economic downturn, a significant interest rate hike).
- Collect the necessary data and assumptions.
- Model the impact of the stress scenarios on the portfolio.
- Analyze the results and identify potential vulnerabilities.
- Potential Pitfalls: Stress tests are based on assumptions, and the actual outcome may differ. The scenarios may not capture all potential risks.
- Step-by-step Procedure:
- Credit Risk Management: Assessing and managing the risk of borrowers defaulting on their loans.
- Step-by-step Procedure:
- Assess the creditworthiness of borrowers.
- Set credit limits and terms.
- Monitor borrowers’ financial performance.
- Take action to mitigate credit risk, such as requiring collateral or restructuring loans.
- Potential Pitfalls: Inaccurate credit assessments can lead to loan defaults. Economic downturns can increase credit risk.
- Step-by-step Procedure:
Project Management Prophylactic Measures
Project managers use prophylactic measures to mitigate risks and ensure projects are completed successfully, on time, and within budget.
- Risk Registers: Creating and maintaining a risk register to document potential risks, their likelihood, impact, and mitigation strategies.
- Step-by-step Procedure:
- Identify potential risks through brainstorming, expert judgment, and historical data.
- Assess the likelihood and impact of each risk.
- Develop mitigation strategies for each risk.
- Assign responsibility for managing each risk.
- Regularly review and update the risk register.
- Potential Pitfalls: Failing to identify all potential risks. Inadequate mitigation strategies.
- Step-by-step Procedure:
- Contingency Planning: Developing plans to address potential risks and ensure the project can continue even if problems arise.
- Step-by-step Procedure:
- Identify potential risks.
- Develop contingency plans for each risk.
- Allocate resources for contingency plans.
- Test the contingency plans.
- Regularly review and update the contingency plans.
- Potential Pitfalls: Inadequate contingency plans. Insufficient resources allocated for contingency plans.
- Step-by-step Procedure:
- Buffer Management: Adding buffers (e.g., time buffers, cost buffers) to the project schedule and budget to absorb potential delays and cost overruns.
- Step-by-step Procedure:
- Estimate the time and cost required for each project task.
- Add buffers to the schedule and budget based on the level of risk.
- Monitor the project’s progress and use the buffers as needed.
- Re-evaluate the buffers periodically.
- Potential Pitfalls: Over-estimation of buffer requirements can lead to inefficiency. Underestimation can lead to delays and cost overruns.
- Step-by-step Procedure:
- Communication Plans: Establishing clear communication channels and protocols to ensure that stakeholders are informed about project progress, risks, and issues.
- Step-by-step Procedure:
- Identify all project stakeholders.
- Determine the communication needs of each stakeholder.
- Develop a communication plan that Artikels the frequency, method, and content of communication.
- Regularly communicate with stakeholders.
- Monitor the effectiveness of the communication plan.
- Potential Pitfalls: Poor communication can lead to misunderstandings, delays, and conflicts. Failure to keep stakeholders informed.
- Step-by-step Procedure:
Healthcare Prophylactic Measures
Healthcare professionals use prophylactic measures to prevent the spread of diseases and protect patients from harm.
- Vaccination: Administering vaccines to stimulate the immune system and provide protection against infectious diseases.
- Step-by-step Procedure:
- Assess the patient’s medical history and any contraindications to vaccination.
- Select the appropriate vaccine.
- Administer the vaccine according to the recommended schedule and route.
- Monitor the patient for any adverse reactions.
- Document the vaccination.
- Potential Pitfalls: Vaccine hesitancy can reduce vaccination rates. Improper storage or administration can reduce vaccine effectiveness.
- Step-by-step Procedure:
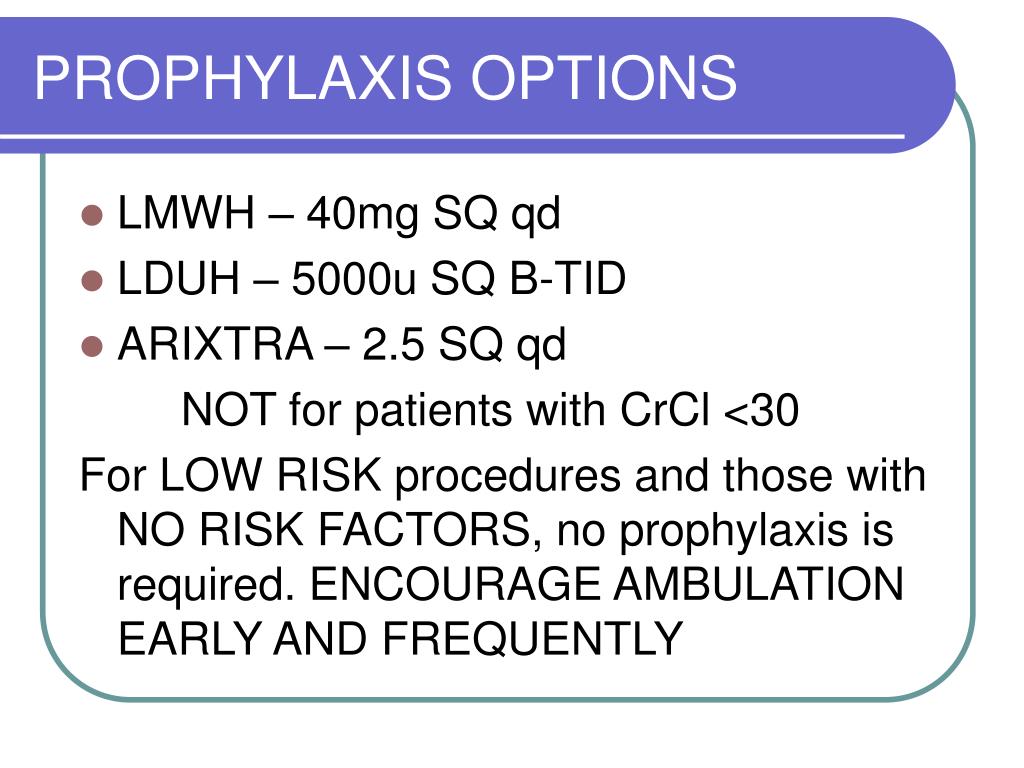
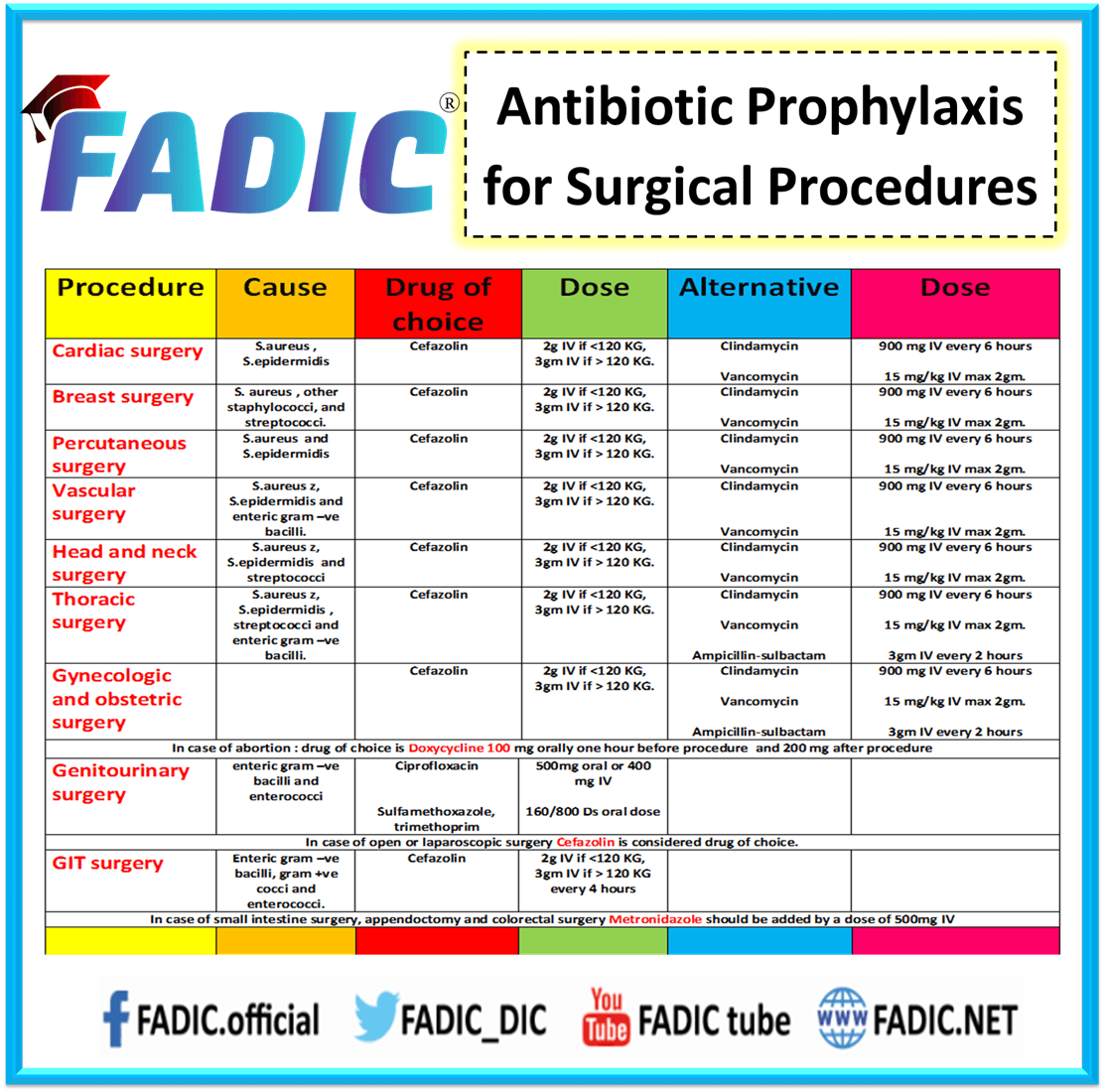
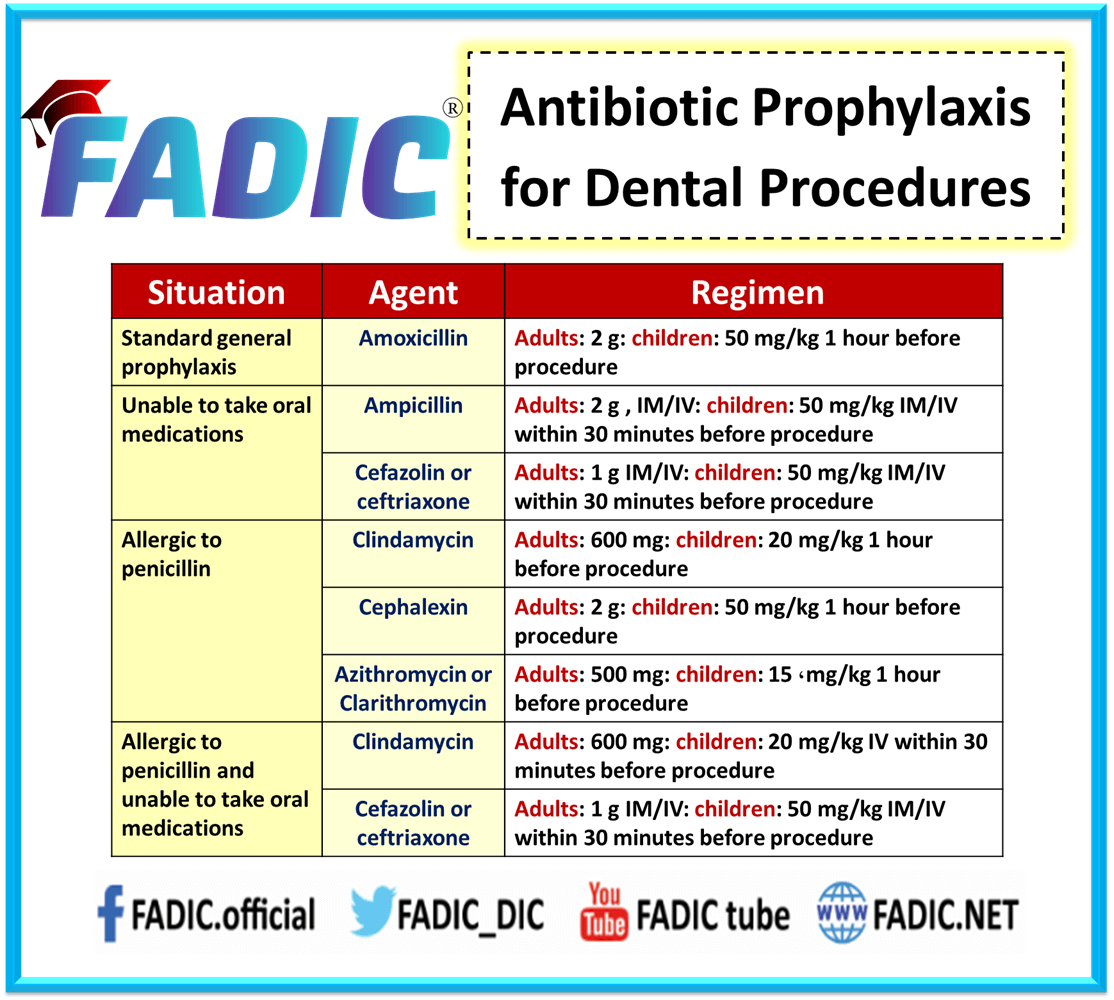
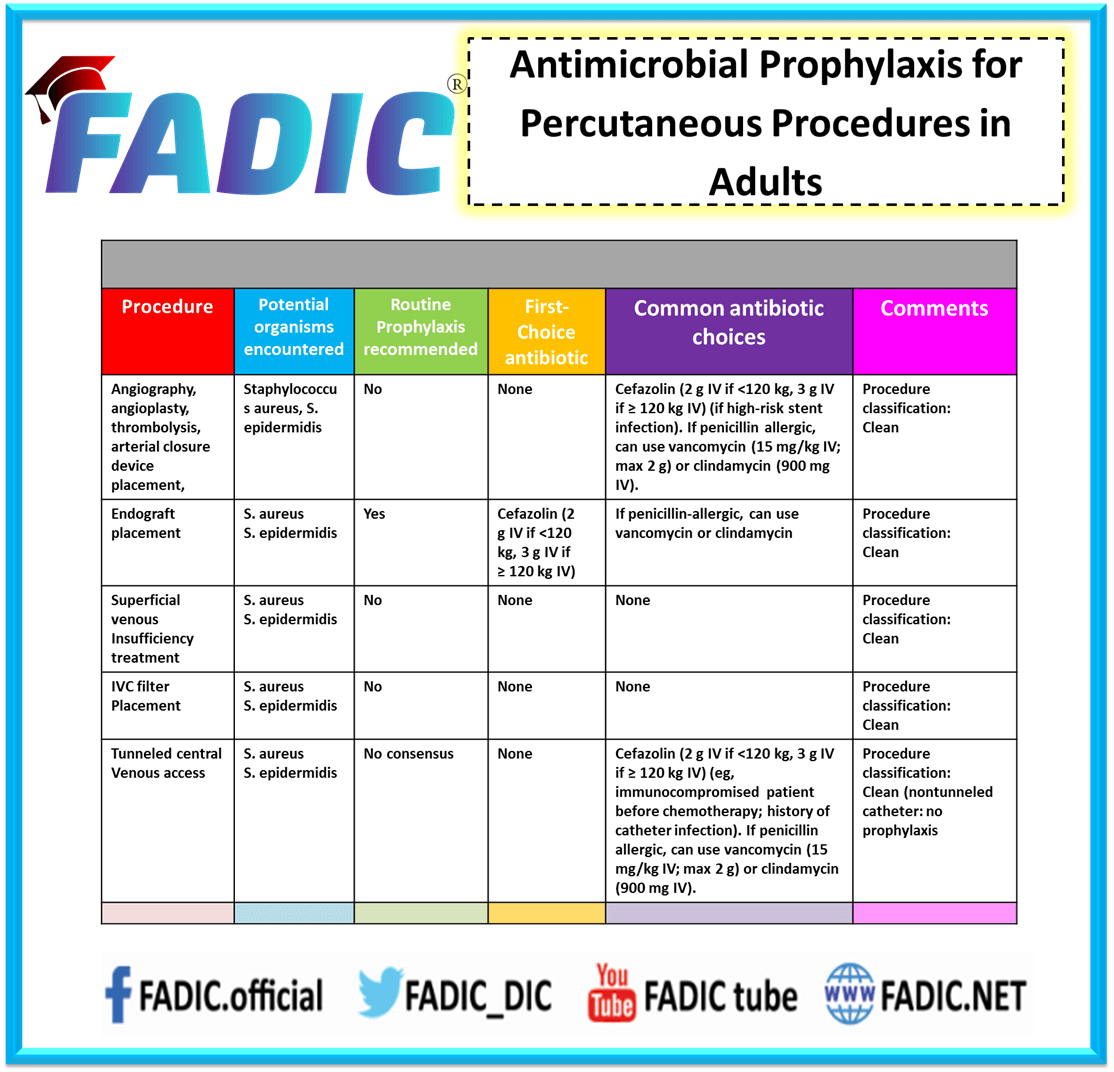
- Antibiotic Prophylaxis: Administering antibiotics to prevent bacterial infections, particularly in high-risk situations, such as surgery or exposure to certain pathogens.
- Step-by-step Procedure:
- Assess the patient’s risk of infection.
- Select the appropriate antibiotic based on the suspected pathogen and the patient’s medical history.
- Administer the antibiotic according to the prescribed dosage and duration.
- Monitor the patient for any adverse reactions.
- Monitor for signs of antibiotic resistance.
- Potential Pitfalls: Overuse of antibiotics can lead to antibiotic resistance. Allergic reactions to antibiotics.
- Step-by-step Procedure:
- Surgical Prophylaxis: Implementing measures to prevent surgical site infections (SSIs), such as preoperative antibiotics, sterile technique, and appropriate wound care.
- Step-by-step Procedure:
- Administer prophylactic antibiotics prior to surgery.
- Ensure proper hand hygiene and sterile technique during surgery.
- Minimize the duration of surgery.
- Provide appropriate wound care post-surgery.
- Monitor the patient for signs of infection.
- Potential Pitfalls: Inadequate adherence to sterile technique. Inappropriate antibiotic selection or timing.
- Step-by-step Procedure:
- Isolation and Quarantine: Separating infected individuals or those exposed to infectious diseases from healthy individuals to prevent the spread of infection.
- Step-by-step Procedure:
- Identify individuals who are infected or have been exposed to an infectious disease.
- Isolate infected individuals from healthy individuals.
- Quarantine individuals who have been exposed to an infectious disease but are not yet showing symptoms.
- Provide appropriate care and support to isolated or quarantined individuals.
- Monitor the spread of the disease.
- Potential Pitfalls: Difficulty in enforcing isolation and quarantine measures. Inadequate resources for providing care and support to isolated or quarantined individuals.
- Step-by-step Procedure:
Prophylaxis in Action
Understanding how prophylaxis works in theory is crucial, but seeing it in action solidifies the concepts. This section dives into real-world examples, showcasing both successful applications and the detrimental effects of neglecting prophylactic measures. By examining these case studies, we can glean valuable lessons to enhance our strategic thinking.
Successful Application: The Cuban Missile Crisis
The Cuban Missile Crisis of 1962 serves as a compelling example of successful prophylactic strategy. The United States, under President John F. Kennedy, faced the imminent threat of Soviet nuclear missiles being deployed in Cuba, posing a direct threat to American security. The U.S. government implemented several prophylactic measures to prevent the Soviets from completing the deployment and escalating the situation to nuclear war.
- Intelligence Gathering: The United States employed extensive intelligence gathering, including U-2 spy plane flights, to confirm the presence of Soviet missiles and assess the progress of their installation. This early warning system was crucial for timely decision-making. The images from the U-2 flights provided irrefutable evidence of the Soviet build-up, allowing the U.S. to take decisive action.
- Naval Blockade (Quarantine): A naval blockade was established around Cuba to prevent further Soviet shipments of offensive weapons. This action, carefully termed a “quarantine” to avoid the connotation of a declaration of war, was a critical prophylactic measure. It aimed to halt the delivery of additional missiles and related equipment.
- Diplomatic Pressure: The U.S. engaged in intense diplomatic negotiations with the Soviet Union, leveraging international pressure and offering concessions to resolve the crisis peacefully. This included a back-channel agreement to remove U.S. Jupiter missiles from Turkey in exchange for the removal of Soviet missiles from Cuba.
- Military Readiness: The U.S. military was placed on high alert, with strategic bombers and other forces prepared for potential military action. This readiness served as a deterrent, signaling the U.S.’s resolve and potentially influencing Soviet decision-making.
The combined effect of these prophylactic measures was the successful removal of Soviet missiles from Cuba. The crisis ended without a nuclear exchange, demonstrating the effectiveness of a well-executed strategy that combined intelligence, decisive action, and diplomatic maneuvering. The United States proactively identified the threat, implemented preventative measures, and ultimately achieved its strategic objectives.
Consequences of Neglect: The Attack on Pearl Harbor
In stark contrast to the Cuban Missile Crisis, the attack on Pearl Harbor in December 1941 offers a tragic example of the consequences of failing to implement adequate prophylactic measures. The United States suffered a devastating surprise attack by the Japanese Navy, resulting in significant loss of life and damage to the Pacific Fleet.The lack of effective prophylaxis contributed significantly to the disaster.
Several critical failures highlighted the shortcomings in pre-emptive planning and risk assessment.
- Intelligence Failures: While the U.S. had intercepted some Japanese diplomatic communications indicating a potential conflict, these were not adequately analyzed or acted upon. The warning signs were present but were not interpreted correctly or disseminated effectively.
- Overconfidence and Complacency: The U.S. military, particularly the Pacific Fleet, exhibited a degree of overconfidence and complacency, believing that a surprise attack was unlikely. This led to a lack of vigilance and preparedness.
- Poor Risk Assessment: The potential for a surprise attack on Pearl Harbor was underestimated. The strategic importance of Pearl Harbor was not fully appreciated, and the necessary defensive measures were not implemented.
- Inadequate Defensive Measures: The U.S. Navy and Army lacked adequate radar coverage, anti-aircraft defenses, and patrol capabilities to detect and deter a surprise attack. The fleet was also concentrated in the harbor, making it a vulnerable target.
The attack on Pearl Harbor underscores the critical importance of identifying potential threats, assessing risks, and implementing appropriate prophylactic measures. The absence of these measures allowed the Japanese to achieve a devastating strategic victory in the initial stages of the war.
Lessons Learned
Both case studies provide valuable lessons for strategic planning. The Cuban Missile Crisis demonstrates the power of proactive measures, while the attack on Pearl Harbor highlights the dangers of complacency and inadequate preparation.The key takeaways include:
- Early Warning is Crucial: Effective intelligence gathering and analysis are essential for identifying potential threats early on.
- Risk Assessment is Paramount: A thorough assessment of potential risks and vulnerabilities is necessary to prioritize prophylactic actions.
- Proactive Measures are Essential: Implementing pre-emptive measures can prevent or mitigate the impact of adverse events.
- Diplomacy and Deterrence: Combining diplomatic efforts with a credible deterrent can effectively manage and resolve crises.
- Preparedness is Key: Maintaining a state of readiness, including robust defensive measures, is critical for protecting assets and interests.
- Learn from Past Mistakes: Analyzing historical events, both successes and failures, can inform and improve strategic decision-making.
These lessons are applicable across various fields, from international relations and military strategy to business and personal life. Prophylaxis, when thoughtfully applied, is a powerful tool for preventing undesirable outcomes and achieving strategic objectives.
Adapting Prophylaxis to Different Environments
The effectiveness of prophylactic strategies is highly dependent on the environment in which they are applied. Environments vary greatly in terms of resources, constraints, and the nature of potential threats. Therefore, a “one-size-fits-all” approach to prophylaxis is rarely successful. Adapting prophylactic measures to the specific context is crucial for maximizing their impact and minimizing wasted effort.
Comparing and Contrasting Prophylactic Strategies Across Environments
Different environments necessitate distinct prophylactic approaches. These differences stem from variations in available resources, the nature of potential threats, and the operational context. Consider the following examples:
- Military Conflict vs. Business Competition: In a military conflict, prophylaxis might involve fortifying positions, establishing supply lines, and conducting reconnaissance to anticipate enemy movements. In business competition, prophylaxis could include market research, intellectual property protection, and developing a strong brand reputation to deter competitors. The goal in both cases is to prevent or mitigate an adversary’s actions, but the specific tactics differ dramatically.
- Healthcare Setting vs. Financial Market: In healthcare, prophylaxis against infectious diseases involves vaccination, sanitation, and hygiene practices. In financial markets, prophylactic measures might include diversification of investments, setting stop-loss orders, and conducting due diligence to prevent losses from market fluctuations or fraud. The risks and corresponding measures are tailored to the specific characteristics of each environment.
- Cybersecurity vs. Physical Security: Cybersecurity prophylaxis includes firewalls, intrusion detection systems, and regular software updates to prevent cyberattacks. Physical security prophylaxis might involve security cameras, access control systems, and security personnel to prevent unauthorized physical access. Both environments involve risk mitigation, but the tools and techniques are distinct.
Modifying Prophylactic Measures Based on Resources and Constraints
The availability of resources and the presence of constraints significantly impact the design and implementation of prophylactic measures. Consider the following scenarios:
- Resource-Rich Environment: In an environment with abundant resources, such as a well-funded organization or a developed country, more comprehensive and sophisticated prophylactic measures can be implemented. This might include advanced technology, extensive training programs, and multiple layers of protection. For example, a corporation with significant financial resources might invest heavily in cybersecurity infrastructure, employ a dedicated security team, and conduct regular penetration testing to identify vulnerabilities.
- Resource-Constrained Environment: In a resource-constrained environment, such as a small business or a developing country, prophylactic measures must be adapted to fit limited budgets and personnel. This might involve prioritizing the most critical threats, utilizing cost-effective solutions, and leveraging existing resources. For instance, a small business might focus on employee training on basic cybersecurity hygiene practices, implementing free or low-cost security software, and using strong passwords to protect their digital assets.
- Time Constraints: Time constraints also impact prophylactic strategies. If rapid action is required, simpler and quicker-to-implement measures might be favored over more complex, time-consuming solutions. For example, in a crisis situation, a company might quickly implement a temporary communication system to ensure employee safety and coordinate emergency response, even if it’s not the most ideal long-term solution.
Dealing with Unexpected Events
Unexpected events are an inherent part of any environment. Prophylactic measures should include contingency plans to address unforeseen circumstances.
“Even the best-laid plans are subject to change. A proactive approach to unexpected events involves identifying potential failure points, establishing backup systems, and training personnel to respond effectively to a variety of scenarios. This includes having clear communication protocols, pre-defined decision-making processes, and the flexibility to adapt to evolving situations. Regular drills and simulations can help prepare for the unexpected and ensure a coordinated response.”
Evaluating the Effectiveness of Prophylactic Measures
Assessing the impact of prophylactic measures is crucial for optimizing their application and ensuring they contribute effectively to preventing your opponent’s plans. This evaluation process involves employing various methods to gauge their success, measure their return on investment (ROI), and refine your prophylactic strategies for improved performance.
Methods for Evaluating Implemented Prophylactic Measures
Several methods can be used to determine how well your prophylactic measures are working. These methods provide data to understand if the actions are achieving their intended goals.
- Incident Rate Comparison: This method involves comparing the frequency of adverse events (the opponent’s successful actions) before and after implementing prophylactic measures. A significant decrease in incidents suggests the measures are effective. For example, if you introduce a prophylactic measure to prevent a specific tactical maneuver, you would track the frequency of that maneuver’s successful execution before and after implementation. A lower frequency after implementation indicates success.
- Qualitative Feedback Analysis: Gathering feedback from team members or other stakeholders involved in implementing or observing the prophylactic measures can provide valuable insights. This feedback can reveal areas of improvement, unforeseen challenges, or positive outcomes that quantitative data might miss. Consider conducting interviews, surveys, or focus groups to collect this information.
- Simulation and Modeling: Using simulations or models to test the impact of prophylactic measures under various scenarios allows for a controlled evaluation. This is particularly useful in complex situations where real-world testing is difficult or risky. For instance, you could simulate different attack vectors an opponent might use and then model how your prophylactic measures would affect their success rate.
- Cost-Benefit Analysis: This involves weighing the costs of implementing and maintaining prophylactic measures against the benefits they provide, such as the potential losses avoided. This can help determine if the measures are economically viable and worth the investment. This can be illustrated using a table:
Category Cost Benefit Implementation Resources spent on implementing a measure Potential losses avoided (e.g., financial, reputational) Maintenance Ongoing costs (e.g., personnel, training) Increased security or efficiency
Measuring the Return on Investment (ROI) of Prophylactic Actions
Calculating the ROI of prophylactic actions helps justify their implementation and provides a basis for comparing the effectiveness of different measures. The ROI quantifies the financial or strategic benefits derived from the investment in prophylactic measures.
- Formula for ROI: The basic formula for calculating ROI is:
ROI = ((Benefit – Cost) / Cost)
– 100Where:
- Benefit represents the value gained from the prophylactic measure (e.g., avoided losses, increased efficiency).
- Cost represents the total cost of implementing and maintaining the prophylactic measure.
- Examples of ROI Calculations:
- Financial ROI: If a prophylactic measure costs $10,000 to implement and saves $50,000 in potential losses, the ROI is ((50,000 – 10,000) / 10,000)
– 100 = 400%. - Strategic ROI: If a prophylactic measure prevents a competitor from gaining a significant market advantage, the ROI could be measured by the value of the market share retained. This could involve estimating the potential revenue gained by retaining that market share.
- Financial ROI: If a prophylactic measure costs $10,000 to implement and saves $50,000 in potential losses, the ROI is ((50,000 – 10,000) / 10,000)
- Challenges in ROI Measurement: Accurately quantifying the benefits of prophylactic measures can be challenging, especially when dealing with intangible assets like reputation or security. Estimating the probability and potential impact of avoided threats is crucial but often involves making assumptions.
Suggestions for Adjusting Prophylactic Strategies Based on Evaluation Results
The evaluation results should be used to refine and optimize prophylactic strategies continually. This iterative approach ensures that measures remain effective and adapt to changing circumstances.
- Iterative Improvement: Prophylactic strategies should be viewed as dynamic and constantly evolving. Regular evaluations provide feedback that informs adjustments, leading to a cycle of improvement.
- Prioritization: If the evaluation reveals that some prophylactic measures are more effective than others, resources should be prioritized accordingly. This might involve allocating more resources to successful measures and re-evaluating or modifying those that are less effective.
- Adaptation: The environment and the opponent’s strategies can change over time. Prophylactic measures should be adjusted to address new threats or vulnerabilities. For example, if an opponent begins to use a new tactic, the prophylactic strategy should be updated to counter it.
- Continuous Monitoring: Establish a system for ongoing monitoring of the effectiveness of prophylactic measures. This could involve regularly reviewing incident reports, collecting feedback, and conducting periodic simulations or tests.
Ethical Considerations in Prophylaxis
Prophylaxis, while a powerful strategic tool, operates within a complex ethical landscape. Employing measures to preempt an opponent’s plans necessitates careful consideration of moral boundaries to avoid unintended harm and uphold ethical principles. This section explores the ethical dilemmas inherent in prophylactic actions.
Identifying Ethical Boundaries in Prophylactic Measures
Establishing clear ethical boundaries is crucial when employing prophylactic measures. These boundaries serve as a moral compass, guiding decision-making and preventing actions that could violate fundamental rights or cause undue harm.
- Respect for Autonomy: Prophylactic actions should, whenever possible, respect the autonomy of the opponent. This means avoiding actions that completely eliminate their ability to make their own choices or pursue their own goals. For instance, preventing a competitor from using a specific marketing strategy is acceptable if it protects the user from harm, but manipulating their decisions through deceptive practices is not.
- Non-Maleficence: The principle of “do no harm” is paramount. Prophylactic measures should be designed to minimize potential harm to the opponent, their stakeholders, and any third parties. This involves carefully assessing the potential consequences of each action and choosing the least harmful option. For example, consider the impact on the opponent’s employees, customers, or partners when implementing a measure to limit their operations.
- Justice and Fairness: Prophylactic strategies should be implemented fairly and justly. This means avoiding discriminatory practices and ensuring that all parties are treated equitably. For example, measures to prevent market manipulation should apply equally to all competitors, regardless of their size or influence.
- Transparency and Accountability: Transparency in the use of prophylactic measures is essential. The rationale behind the actions should be clear, and the actions themselves should be accountable. This involves being open about the goals and the methods used, and being prepared to justify the actions if challenged. Consider a situation where a company is using security measures to prevent data breaches; they should inform their users about the measures being taken.
Potential for Unintended Consequences of Prophylactic Actions
Prophylactic actions, even when well-intentioned, can have unintended consequences. These consequences can range from minor inconveniences to significant harms, and it is crucial to anticipate and mitigate these risks.
- Chilling Effects: Prophylactic measures can sometimes have a “chilling effect,” discouraging legitimate activities. For instance, overzealous enforcement of anti-spam measures might inadvertently block legitimate emails, hindering communication and collaboration.
- Escalation of Conflict: Prophylactic actions can be perceived as aggressive or provocative, potentially leading to an escalation of conflict. For example, a preemptive cyberattack, intended to prevent a future attack, could be misinterpreted as an act of war, prompting retaliation.
- Unforeseen Side Effects: Prophylactic measures can have unforeseen side effects that impact other areas. For instance, a measure to restrict the flow of information might inadvertently stifle innovation or limit access to essential resources.
- Erosion of Trust: If prophylactic actions are perceived as unfair or manipulative, they can erode trust between parties. This can damage relationships and undermine cooperation.
Illustration: The Ethical Dilemmas of Prophylaxis
Imagine a scenario involving two competing pharmaceutical companies, “NovaPharm” and “VitaCorp,” developing a groundbreaking new drug to treat a rare disease. NovaPharm discovers that VitaCorp is planning to release a generic version of the drug immediately after NovaPharm’s patent expires, significantly impacting NovaPharm’s market share and profitability. NovaPharm considers several prophylactic measures.
Illustration Description: The illustration depicts a divided image. On the left side, we see NovaPharm’s headquarters, a modern glass building. A graph displays a sharp decline in revenue, symbolizing the potential impact of VitaCorp’s generic drug. A NovaPharm executive, looking concerned, is studying the graph. On the right side, we see VitaCorp’s laboratory.
A team of scientists is working diligently. A thought bubble above one of the scientists shows the release date of the generic drug. A split down the middle emphasizes the opposing sides, while a scale in the middle represents the ethical considerations.
The scale represents the following options, weighing the potential benefits against the ethical concerns:
- Option 1: Lobbying for Extended Patent Protection: This involves NovaPharm using its resources to influence lawmakers to extend the patent duration.
Ethical Considerations:
- Potential Benefit: Protects NovaPharm’s investment and market share, allowing for further research and development.
- Potential Harm: Delays access to the potentially life-saving drug for patients, potentially increasing healthcare costs.
- Option 2: Public Relations Campaign: Launching a campaign to discredit VitaCorp’s generic drug, highlighting perceived safety concerns.
Ethical Considerations:
- Potential Benefit: Reduces consumer confidence in VitaCorp’s drug, protecting NovaPharm’s market share.
- Potential Harm: Spreads misinformation, potentially harming VitaCorp’s reputation and possibly influencing patients’ health decisions.
- Option 3: Strategic Delay Tactics: Engaging in legal maneuvers or regulatory delays to slow down VitaCorp’s generic drug approval process.
Ethical Considerations:
- Potential Benefit: Buys NovaPharm more time to market its own product.
- Potential Harm: Limits patient access to potentially more affordable medication, and could be considered an abuse of legal processes.
The illustration highlights the complexities of prophylaxis. While protecting NovaPharm’s interests is a valid business goal, each prophylactic measure presents ethical challenges. The executive must weigh the potential benefits against the potential harms, considering the principles of autonomy, non-maleficence, justice, and transparency to make a responsible decision.
Conclusion
In conclusion, mastering How to Use Prophylaxis to Prevent Your Opponent’s Plans empowers you to transform from a reactive player to a proactive strategist. By understanding your opponent, anticipating their moves, and implementing preemptive measures, you can significantly increase your chances of success. Embrace the power of foresight, and turn the tables on your adversaries by taking control of the game.